0x protocol decentralized exchange
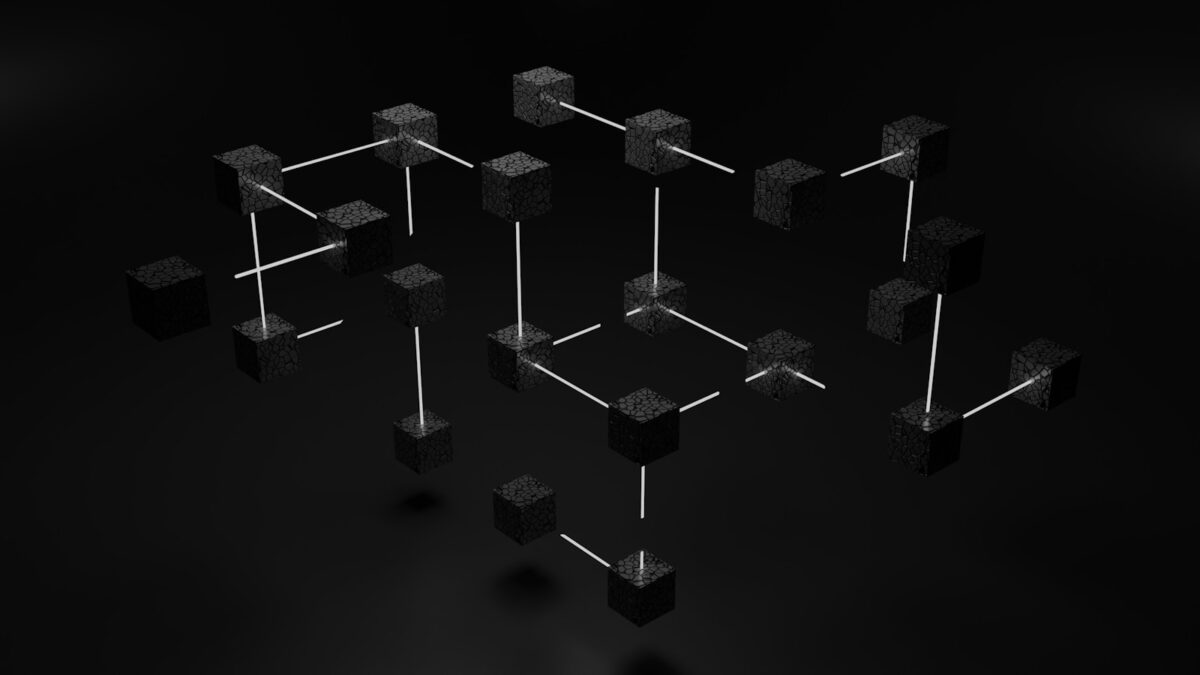
0x introduces an innovative framework that enables peer-to-peer token swaps without relying on centralized intermediaries. By leveraging off-chain order relay combined with on-chain settlement, this system significantly reduces transaction costs and enhances scalability. The core design involves participants broadcasting signed orders, which relayers collect and publish, creating a dynamic marketplace of offers ready for execution. […]